The ‘Debian Testing branch’ is the basic and the root of the Kali Linux. The Debian repositories are mainly imported the most of the packages Kali uses. Kali Linux famously grew when it was a character in different episodes of the TV series. Tools highlighted in the show.
Overview of Kali Linux Download ISO
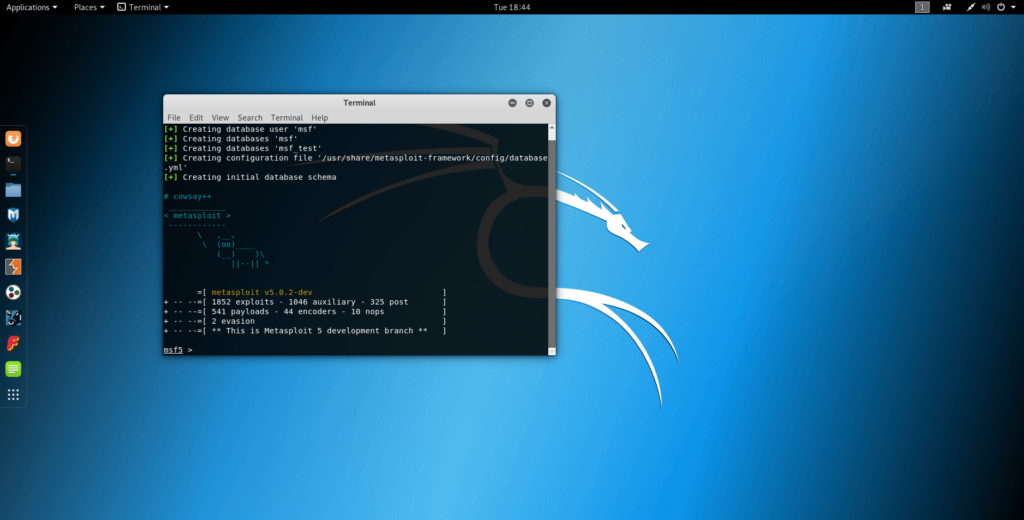
Kali Linux is mainly built for forensics of any kind of digital image or something else. It is useful for penetration testing also. This kali Linux keeps up and is funded by Offensive Security. Those companies are also farming for ‘penetration testing and digital forensics’.
This American company is Operating these from around 2007. This company constructs its open-source projects. This project is now advanced with its security courses and of course the Kali Linux distribution. Mati Aharoni was first started by this American company. They also employ security professionals with experience in security penetration testing. The company has offered security counseling also.
In this case, swap space and auto mounting are disabled. Sometimes, the developers recommend particular users to examine these features. These are mainly done extensively before using Kali for real-world forensics’.
Recommended Post:- Dual Boot Kali Linux With Windows 10
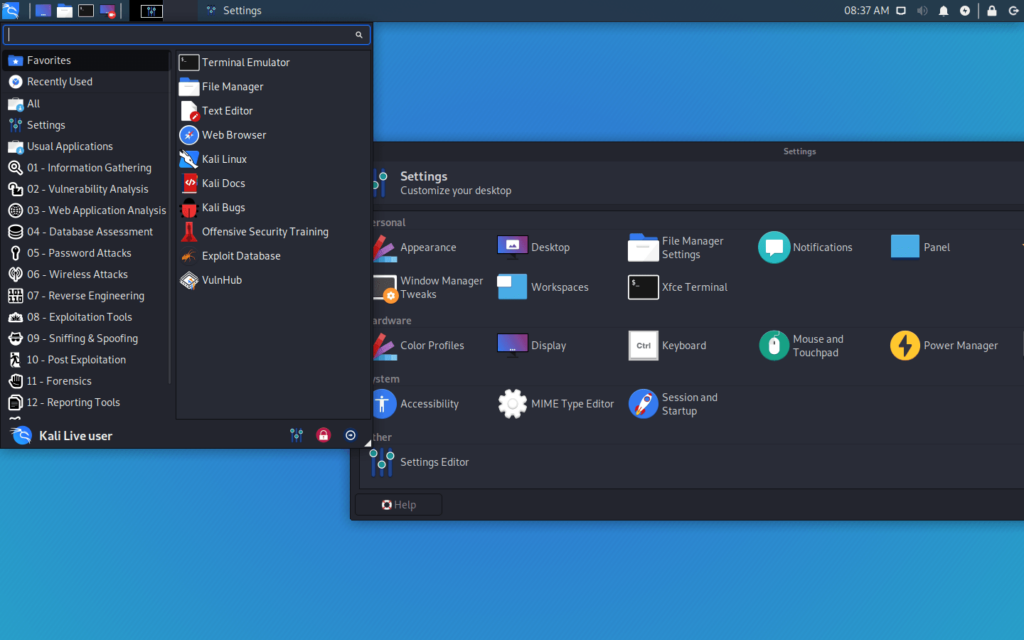
Features of Kali Linux Download ISO
Kali Linux is the first Open Source Android penetration testing platform. This version is only for Nexus devices. Besides, Bad USB MITM attacks are also present. Kali Linux has a dedicated project set is a setting which is mainly aside for compatibility in the Kali Linux.
- The porting feature to specific Android devices which is called Kali NetHunter.
- This version has another feature that is one-click MANA Evil Access Point setups’ which is very useful for users.
- HID keyboard is another feature of it which has the Teensy like attacks.
Download Process of Kali Linux Download ISO
We have come up with some easy steps of downloading and installing a Kali Linux. We would suggest you to follow the below instructions carefully to avoid failure.
- Users have to be very sure that they have got Kali Linux, which is a professional penetration test. It is used as a professional toolkit also. After confirmation, the user may further proceed to run Kali Linux live & install it to their hard disk. As Kali Linux is called the penetration tester, it has proper confidence in the integrity of users’ tools which is critical. The user’s investigation would not be reliable.
- Sometimes a bogus version of Kali Linux may dangerously damage which is called Kali’s strength, which is used as a leading penetration testing distribution. Many people want to stick with many reasons to stay sketchy. These resemble Kali. Users are not interested to find the original version instead of using the fake site.
- Users may only download the Kali Linux from the official website other than the fake site. The site is ” https://www.kali.org/downloads“. Users may not be able to browse the pages without using SSL. The connection makes more tuff for attackers to buy the encryption technique.
- So, attackers can not use” man- in- the- middle” to change users’ downloads. If the check the sections on verifying the download with the “SHA256SUMS” file, where they can find some potential weakness
- If the user may download an image from the original site, then the user has to run it. Users have to verify its checksum for confirming that it is supported or not.
- There present different methods where users can verify their downloads. Each method assures the user up to a definite level.
- An ISO image can be downloaded by the official Kali Linux site by the user.
- Users may calculate the ISO’s SHA256 hash. It is compared by inspection with the value. The value is enlisted on the Linux site.
- This is potentially susceptible to subversion which is via DNS poisoning. Without it, this is a very good and fast version.
- Users can download an ISO image through the torrent site. This site will pull down the file which is unsigned. The file contains the calculated SHA256 signature. Users may also use the shasum command. The user also can automatically verify the files which have the computed signature will match the secondary file. This process has many cons.
- If the user may pull down the torrent site then they are not properly working as Kali Linux. But then they possess a good signature.
- Users can download the cleartext signature file and the same version file as the user wants to download the Kali Linux which has to obtain its real thing. The same version of cleartext which signed with the official Kali Linux private key.
- This key mainly relates to GNU privacy which guards first. This may verify the computed SHA256 signature. It must be matched with the clear. It must be verified by the signed version of the file containing SHA256 hash as this has been correctly signed with the official key.
System Requirements of Kali Linux Download ISO
- The Version of 2020.2 demands at least 3.6 GB.
- 257MB RAM is required for i386 as the minimum range. Their AMD64 architectures are also required.
- A bootable CD-DVD drive is also required for the KALI Linux. They’re also a need for a USB stick.
- Official Kali Linux VMware Images which is called the “ARM Images”:
- ARM-based devices – The hardware architecture is very considerable. So, having a single image is impossible.
Download Kali Linux
We hope that you are satisfied with the information we have delivered to you. If you are a Linux user then you should be way familiar with the system and it won’t take much time to understand the behavior of Kali Linux. This application has a good amount of feasibility while operating. Also, after installing Kali Linux will get extremely handy and easy to function.
Learn additional features and functionalities in your operating system up-to-date. If you have any queries regarding the Kali Linux you can drop down your concern in the comment section and we will get back with the solution in minimum time.




