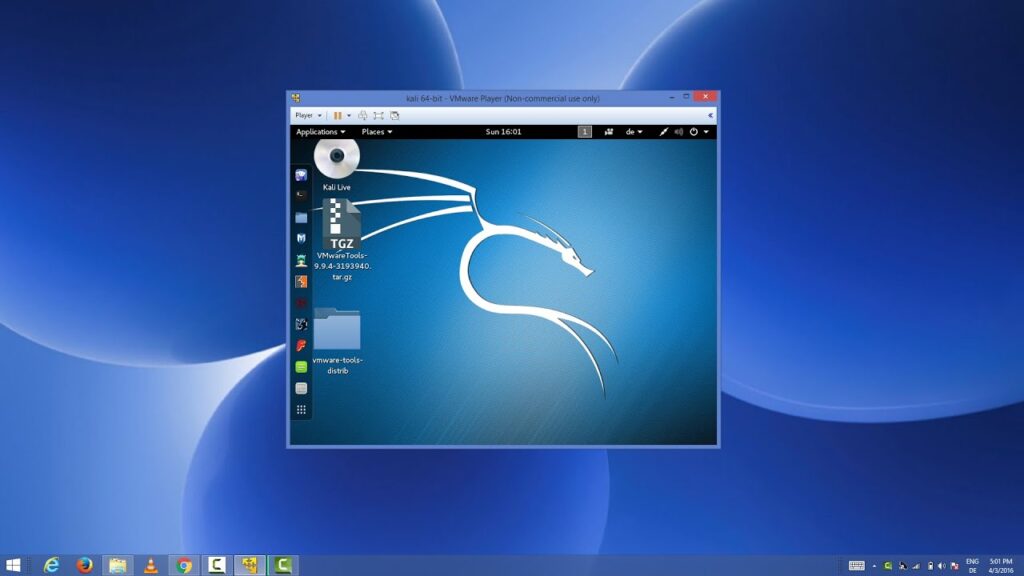
Kali Linux may be a very powerful OS with a plethora of preinstalled tools that will possibly destroy computers, network infrastructure, and if used improperly or unethically, can cause actions that will be perceived as criminal or lawbreaking.
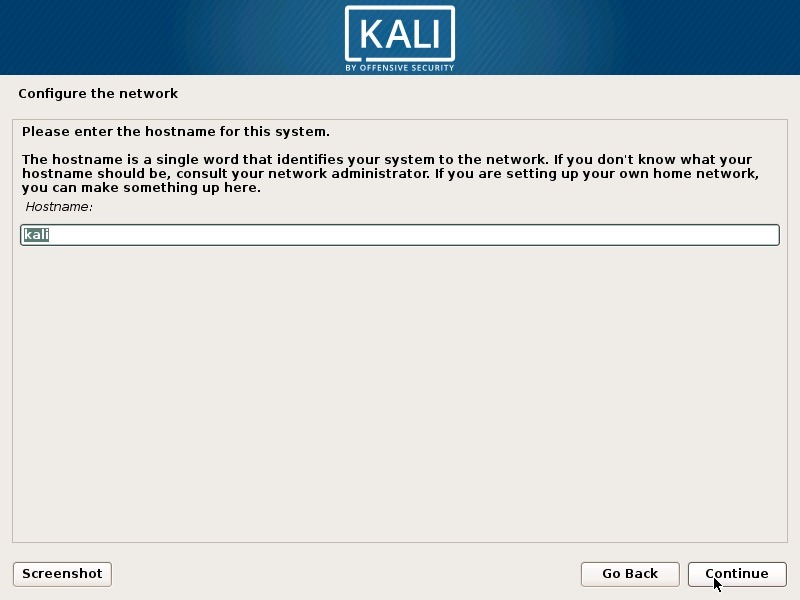
For this reason, passwords are essential. While passwords are the foremost basic security practice, many administrators and security professionals often forget or ignore the utilization of passwords. Basic security practices such as proper use of passwords are essential to make sure that your installation of Kali Linux isn’t employed by others who might inadvertently or maliciously cause harm to an individual, computer, or network.
Installing operating systems, like Microsoft’s Windows, Apple’s OSX, or open-source platforms like Debian and Ubuntu, could also be a habit to some, but a refresher on this process is usually good. people who haven’t installed an OS before shouldn’t worry, the subsequent sections.
Kali Linux is exclusive in some ways, but the foremost important distinctions of this distribution are the power to not only run from a tough drive installation but also boot as a live disk and therefore the number and sort of specialized applications installed by default. A live disk is an OS installed on a disk including Compact Disks (CDs), Digital Video Disk (DVD), or Blu-Ray Disk. As a penetration tester, the power else a live disk is sort of important.
Also Read:- How to Install Debian 9 on VMware Workstation on Windows
Overview of Kali Linux
Those with access to local machines on the network can leverage live disks to use these machines albeit the penetration tester doesn’t have an account on the installed OS. The system will boot to the live disk instead of the local hard drive; that’s if the machine is configured correctly the penetration tester will then have access to several of the resources on the local network, while at an equivalent time not leaving evidence on the local machine’s disk drive.
The software installed on Kali Linux is one more reason it is uniquely outfitted for the penetration tester. By default Kali Linux has 400 penetration testing and security tools, packages and applications installed and has the power to feature more as they’re needed.
Selecting Hard Drive Platform for Information
Traditionally, the OS is installed on the computer’s disk drive, however, with operating systems like Kali Linux, there’s a capability to install the OS to thumb drives (aka flash drives) and SD cards due to the recent, availability, and affordability of larger capacity devices. Regardless of the memory device is employed to put in the OS, it is critical to work out whether to put into a standalone computer (such as a lab computer) or a laptop which will leave a mobile solution?
If very specific hardware, like high-powered graphics cards, is going to be used for cracking passwords, it’s recommended that the installation of Kali Linux be installed on a personal computer. If there’s a requirement to hold the operating system from the customer site to the customer site, or there’s a desire to check wireless devices, a laptop is suggested. The installation of the OS is the same for laptop and desktop computers.
Partitioning is the act of separating out the filing system to specific areas of the hard drive by setting special block sizes and sectors. Partitioning can prevent an OS from becoming corrupted by log files that take over a system and under certain circumstances provide greater security. The OS is, at the essential level, already broken into two different partitions.
The first partition is the swap area, which is employed for memory paging and storage. A second partition is designated for everything else and is formatted with a file structure like the extended filing system 3 (ext3) or extended file system 4 (ext4). within the case of laptops, especially those devices where the operating system is going to be reloaded time and time again, further partitioning is not necessary. For customized installations or computers that will have a more persistent OS, there’s a requirement to a minimum of filter the temporary (temp) files.
Partitioning the Hard Drive
Not to overuse the phrase, but “Size does matter.” A general rule of thumb is the bigger the drive, the higher. This book is recommending a drive with a minimum of 120GB of space; however, even this will become full very quickly, especially within the case of password cracking and forensics or pentesting projects that need tons of control over, evidence, logs and report generation or collection. within the case of most commercial and agency security assessments.
The OS is cleaned, erased, or completely removed to maintain a long time baseline environment. This practice is widely accepted throughout the safety community thanks to the necessity for the correct handling of customer confidential data and minimizing spillage of corporate information that would possibly harm the company’s infrastructure or reputation.
System requirements of Kali Linux
- Require 3GB hard disk space
- Require 512 MB RAM
- Require CD-DVD drive/USB stick